In Part 1, we explored how geopolitical tensions can translate into cyber operations targeting enterprise environments.
Groups like Handala operate in a space where cyber operations serve both disruption and narrative influence, combining technical intrusions with public messaging. But for security teams, the most important question is not political.
It is operational. If this campaign appeared inside your environment tomorrow, would your controls detect it before impact?
To answer that, we need to move from campaign analysis to detection engineering, and understand what telemetry and controls are actually required for those detections to work.
What Was Actually Confirmed
Let’s start with facts. Based on the public filing by Stryker Corporation:
| Area | Confirmed Detail |
|---|---|
| Detection | Incident identified on March 11, 2026 |
| Impact | Disruption to Microsoft environment |
| Response | Cyber response plan activated, external experts engaged |
| Malware | No confirmed ransomware or traditional malware |
| Status | Contained, investigation ongoing |
That’s all we know for certain.
- No confirmed entry point.
- No confirmed toolset.
- No confirmed payload.
Everything else must be treated carefully. Not as fact, but as informed assessment based on known threat behaviour. And that’s where intelligence starts to matter.
Threat Actor Snapshot
Before we go deeper, we anchor the discussion.
ThirdEye Intel Actor Tracking
- Actor ID: TEI-ACT-001
- Actor Name: Handala
- Aliases: Void Manticore, Red Sandstorm, Banished Kitten
- Origin: Iran, suspected MOIS alignment
- Actor Class: Statecraft Actor
- Primary Objective: Disruption and psychological signalling
Active since at least July 2023, Handala operates in a way most environments would not immediately flag.
- Credential access.
- Lateral movement.
- Then impact.
Simple on paper. Difficult in practice.
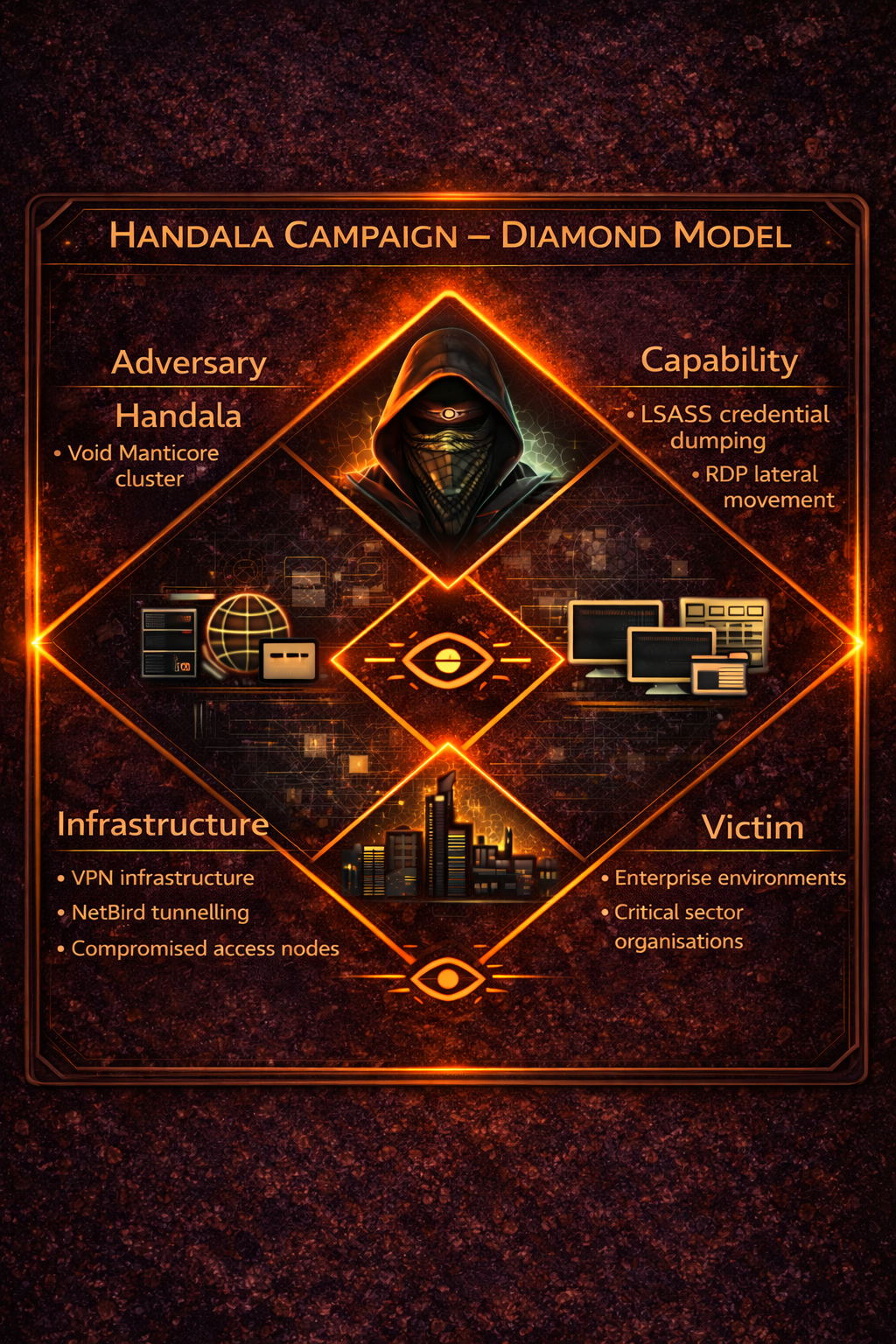
Diamond Model View of the Campaign
The Diamond Model helps simplify what is otherwise messy.

| Element | Observed Characteristics |
|---|---|
| Adversary | Handala / Void Manticore |
| Infrastructure | VPN nodes, tunnelling infrastructure |
| Capability | Credential dumping, RDP movement, destructive execution |
| Victim | Enterprise environments, critical sectors |
The key insight sits in the capability layer. This is not malware-heavy. This is behaviour-heavy. Which means detection must focus on what the attacker does, not what they run.
What Handala’s Tradecraft Suggests
The pattern is not complex. That’s the problem.
| Behaviour Category | Observed Pattern |
|---|---|
| Intrusion style | Hands-on-keyboard |
| Access method | Credential-driven |
| Tooling | Native / legitimate utilities |
| Network behaviour | Encrypted tunnelling |
| Objective | Controlled disruption |
No noise at the start, just quiet movement which then leads to the part most teams underestimate – The sequence.
Behaviour Chain Observed in the Campaign
When you step back, the pattern becomes clear.

Nothing here is new. Which is exactly why it works.
From MITRE to Reality
The following techniques are mapped based on observed Handala tradecraft across different campaigns. Not all are publicly confirmed in the Stryker incident, but they represent the most realistic defensive lens.
MITRE + Detection + Telemetry + Mitigation
| Technique | ID | Behaviour | Detection Signal | Required Telemetry | Mitigation |
|---|---|---|---|---|---|
| Credential Dumping | T1003.001 | LSASS memory access | Sysmon Event 10 | LSASS monitoring | Privileged Process Integrity |
| RDP Movement | T1021.001 | Remote login across hosts | Event 4624 Type 10 | Security logs | MFA + segmentation |
| PowerShell Execution | T1059.001 | Script execution | Event 4104 | Script block logging | Execution control |
| Protocol Tunnelling | T1572 | Encrypted internal tunnel | New interface + traffic | Network + endpoint logs | Network monitoring |
| Data Destruction | T1485 | File deletion activity | High-volume operations | EDR telemetry | Backup + monitoring |
MITRE is only useful when it answers one question: What would this look like in my logs?
Threat Hunting Package — Handala Tradecraft
This is where intelligence becomes usable.
Hunting Objectives
| Objective | Description |
|---|---|
| Detect credential access early | Identify LSASS interaction |
| Identify lateral movement | Track RDP behaviour |
| Detect hidden access paths | Identify tunnelling activity |
| Detect impact staging | Identify destructive execution |
Hunting Hypotheses
| Hypothesis | What to Look For |
|---|---|
| Credential access precedes movement | LSASS access events |
| Tunnelling bypasses segmentation | New network interfaces |
| Lateral movement creates patterns | RDP spikes |
| Destruction follows escalation | PowerShell + file activity |
Hunting Accelerators – Example Detection Logic
These examples are simplified and must be tuned for your environment.
LSASS Access Indicator
EventID: 10TargetImage: lsass.exeGrantedAccess: suspicious valuesRDP Movement Pattern
EventID: 4624LogonType: 10Look for:
- same user across multiple hosts
- short time window
- privileged accounts
PowerShell Suspicious Execution
Image: powershell.exe (note that the name can be changed like ps.exe)CommandLine: encoded or obfuscated patternsNetwork Tunnelling Behaviour
CommandLine contains: tun / tap / wireguard indicatorsBehaviour Correlation Analytics – From Signals to Story
Single alerts don’t tell the story. Sequences do.
1. TEI-CORR-001 – Credential Access → Lateral Movement
Detection Logic
LSASS access detected→ followed by RDP logon (LogonType 10)→ within short time window (e.g. 15–30 mins)What this indicates
- credential dumping likely successful
- attacker beginning lateral movement
Sample Sigma-style Concept
title: TEI-CORR-001 Credential Access Followed by RDP Movementid: tei-corr-001status: experimentalauthor: ThirdEye Intellogsource: product: windowsdetection: lsass_access: EventID: 10 rdp_logon: EventID: 4624 LogonType: 10 timeframe: 30m condition: lsass_access followed_by rdp_logonlevel: criticalWhy this works
- LSASS access alone can be noisy.
- RDP logon alone is normal.
👉 Together, they indicate progression.
2. TEI-CORR-002 – Lateral Movement → Administrative Execution
Detection Logic
Multiple RDP logons→ followed by PowerShell execution→ using elevated privilegesSample Sigma-style Concept
title: TEI-CORR-002 RDP Movement Followed by PowerShell Executionid: tei-corr-002status: experimentalauthor: ThirdEye Intellogsource: product: windowsdetection: rdp_activity: EventID: 4624 LogonType: 10 powershell_exec: Image|endswith: - '\powershell.exe' - '\pwsh.exe' suspicious_flags: CommandLine|contains: - '-enc' - 'Invoke-Expression' timeframe: 20m condition: rdp_activity followed_by powershell_execlevel: highWhy this works
Movement followed by execution is a strong indicator of:
👉 attacker expanding control
👉 preparing for impact
3. TEI-CORR-003 – Hidden Access → Internal Expansion
Detection Logic
New network interface (tunnel)→ followed by new internal connections→ not seen in baseline behaviourSample Sigma-style Concept
title: TEI-CORR-003 Tunnel Establishment Followed by Internal Accessid: tei-corr-003status: experimentalauthor: ThirdEye Intellogsource: product: windowsdetection: tunnel_activity: CommandLine|contains: - 'tun' - 'tap' - 'wireguard' lateral_connection: EventID: 4624 timeframe: 30m condition: tunnel_activity followed_by lateral_connectionlevel: highWhy this works
This identifies:
👉 segmentation bypass
👉 hidden internal foothold
4. TEI-CORR-004 – Pre-Impact Destructive Pattern
Detection Logic
Privilege escalation→ PowerShell execution→ high-volume file operationsSample Sigma-style Concept
title: TEI-CORR-004 Pre-Destruction Behaviour Patternid: tei-corr-004status: experimentalauthor: ThirdEye Intellogsource: product: windowsdetection: powershell_exec: Image|endswith: - '\powershell.exe' file_activity: EventID: 4663 timeframe: 15m condition: powershell_exec followed_by file_activitylevel: criticalWhy this works
This is the last opportunity to detect:
👉 destructive intent before impact
Detection improves when we stop looking at events in isolation and start recognising behaviour as a sequence.
Detection Telemetry – Getting Specific
“Enable PowerShell logging” is not enough.
PowerShell Visibility
| Signal | Event |
|---|---|
| Script Block Logging | 4104 |
| Module Logging | 4103 |
| Transcription | Full session |
| AMSI | EDR |
Core Telemetry
| Behaviour | Source | Event |
|---|---|---|
| LSASS access | Sysmon | 10 |
| Process execution | Sysmon | 1 |
| RDP login | Security | 4624 |
| RDP session | Terminal Services | 1149 |
| GPO changes | AD | 5136 |
Microsoft / Intune Layer
| Area | Focus |
|---|---|
| Device configuration | Policy changes |
| Compliance logs | Device anomalies |
| Application deployment | Payload delivery |
| Admin activity | Privilege misuse |
Building a Detection Library from This Analysis
Threat intelligence should not end in a report. It should result in:
- detection rules
- telemetry improvements
- hunting hypotheses
This is how intelligence becomes operational.
From Intelligence to Capability – Where SOCtane Fits
One of the biggest challenges is not intelligence. It is execution.
- We map.
- We detect.
- We hunt.
But over time, it fragments. That’s where SOCtane comes in. Not as a dashboard. But as a threat management layer that connects:
- intelligence
- detection
- telemetry
- response
Every actor is translated into:
- detection logic
- telemetry requirements
- hunting models
- control gaps
This follows the ThirdEye Threat Management Model (TTMM):
Threat Intelligence↓ATT&CK Mapping↓Detection Engineering↓Telemetry↓ControlsSOCtane also uses AI to assist in:
- identifying behaviour patterns
- correlating signals
- suggesting detection improvements
Not replacing analysts but accelerating them where it matters. Because speed without context creates noise. And context without speed creates risk.
Final Thought
Most attacks don’t begin with impact they begin quietly.
- A process touches memory.
- A login looks normal.
- A session starts somewhere it shouldn’t.
Individually, nothing stands out. Together, they tell a story. The question is not whether the signals exist. It is whether we are seeing them early enough.
Because cybersecurity isn’t just a practice — it’s a reflection of character.