Defending Against the Handala Campaign
In Part 1, we explored how geopolitical tensions can translate into cyber operations targeting enterprise environments.
Groups like Handala operate in a space where cyber operations serve both disruption and narrative influence, combining technical intrusions with public messaging. But for security teams, the most important question is not political.
It is operational. If this campaign appeared inside your environment tomorrow, would your controls detect it before impact? To answer that, we need to translate threat intelligence into something defenders can actually use.
This means moving from campaign analysis to detection engineering, and understanding what telemetry and controls are required for those detections to work.
Threat Actor Snapshot
Before diving into the defensive perspective, it helps to anchor the discussion in the actor we are analysing.
ThirdEye Intel Actor Tracking
- Actor ID: TEI-ACT-001
- Actor Name: Handala
- Aliases: Void Manticore, Red Sandstorm, Banished Kitten
- Origin: Iran (suspected MOIS alignment)
- Actor Class: Statecraft Actor
- Primary Objective: Disruption and psychological signalling
Handala has been active since at least July 2023, operating primarily through intrusion campaigns designed to create visibility and disruption rather than purely financial outcomes. Their recent activity demonstrates a pattern familiar to many enterprise defenders.
- Credential access.
- Lateral movement.
- Then impact.
Understanding how those stages connect is critical for detection.
Diamond Model View of the Campaign
The Diamond Model of Intrusion Analysis provides a useful way to understand how the campaign operates.
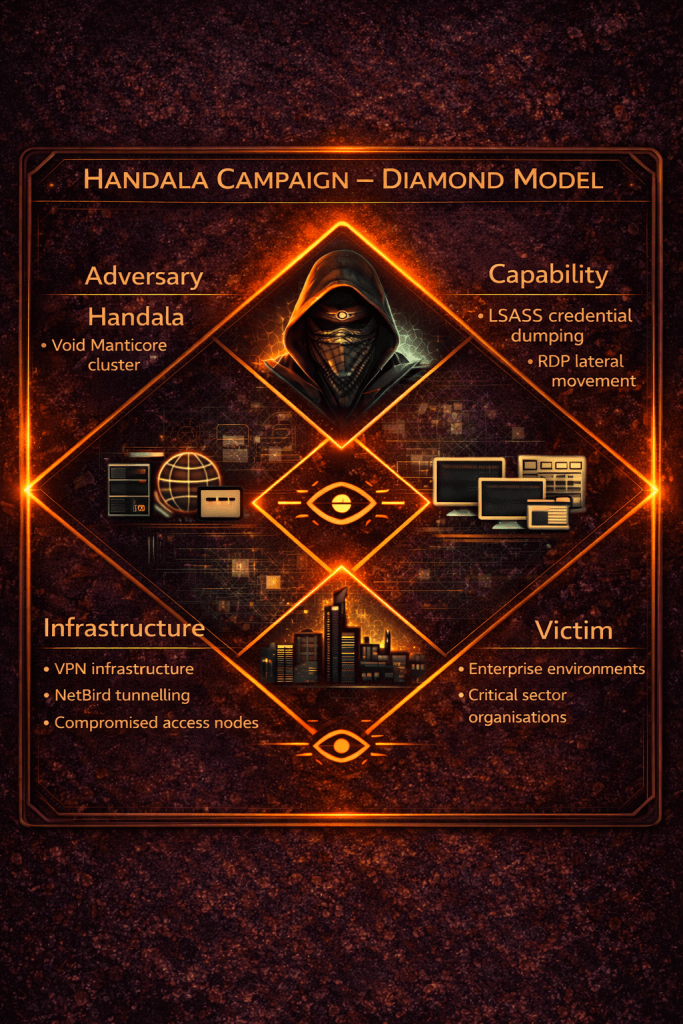
| Element | Observed Characteristics |
|---|---|
| Adversary | Handala / Void Manticore cluster |
| Infrastructure | VPN nodes and tunnelling infrastructure |
| Capability | credential dumping, RDP lateral movement, destructive payload distribution |
| Victim | enterprise environments and critical sectors |
Handala Campaign Diamond Model
The capability layer is particularly important for defenders. Unlike traditional malware campaigns, much of the activity relies on legitimate administrative mechanisms already present inside enterprise networks.
That means detection must focus on behaviour rather than malware signatures.
Key Tradecraft Observed
Across multiple investigations and public reporting, the campaign demonstrates several recurring behaviours.
- Credential dumping through LSASS memory access.
- Extensive RDP based lateral movement.
- Use of tunnelling tools to maintain internal connectivity.
- Modification of Group Policy objects to distribute scripts.
- Destructive activity including data deletion or system wiping.
Individually these behaviours may appear routine in enterprise environments. Together they form a recognisable intrusion pattern.
To understand that pattern more clearly, we can map the activity to MITRE ATT&CK.
MITRE ATT&CK Techniques
| Tactic | Technique | ID |
|---|---|---|
| Credential Access | OS Credential Dumping: LSASS Memory | T1003.001 |
| Execution | PowerShell | T1059.001 |
| Execution | Windows Management Instrumentation | T1047 |
| Lateral Movement | Remote Desktop Protocol | T1021.001 |
| Persistence | Account Manipulation | T1098 |
| Impact | Data Destruction | T1485 |
| Impact | Disk Structure Wipe | T1561 |
These techniques highlight a critical observation. The campaign relies heavily on identity abuse and administrative tools, which means defensive controls should prioritise identity visibility and endpoint telemetry.
MITRE Mitigations Relevant to the Campaign
MITRE also provides a catalogue of mitigations aligned to these techniques.
| Mitigation | Purpose |
|---|---|
| Privileged Account Management | restrict and monitor administrative access |
| Privileged Process Integrity | prevent unauthorised LSASS access |
| Execution Prevention | restrict unauthorised scripting |
| Network Segmentation | limit lateral movement pathways |
| Multi-Factor Authentication | protect identity infrastructure |
In many destructive campaigns, attackers do not begin by deploying malware. They begin by taking control of identity infrastructure. Once that happens, destructive actions become significantly easier.
Translating Intel into Detection Telemetry
Threat intelligence becomes actionable only when defenders can observe the behaviours described in a campaign. A common challenge for many organisations is that the required telemetry simply does not exist. The following table maps observed techniques to the telemetry required for detection.
| Technique | Detection Signal | Required Telemetry | Control Required |
|---|---|---|---|
| LSASS credential dumping | process accessing LSASS memory | Sysmon Event ID 10 | Sysmon configured for process access monitoring |
| LSASS dump via comsvcs | rundll32 loading comsvcs.dll | Sysmon Event ID 1 | endpoint process creation logging |
| privileged session creation | new administrative logon | Windows Event ID 4624 | advanced audit logon policy |
| RDP lateral movement | remote interactive logons | Event ID 4624 LogonType 10 | RDP authentication logging |
| RDP session creation | terminal services connection | Event ID 1149 | Terminal Services logging enabled |
| Group Policy modification | directory object modification | Event ID 5136 | Active Directory auditing |
| remote command execution | WMI or PowerShell activity | Sysmon / PowerShell logs | script block logging |
This mapping illustrates an important principle. Detection rules cannot function without the telemetry required to support them.
Endpoint and Identity Controls
Several defensive controls significantly improve visibility into campaigns like this.
Endpoint telemetry configuration
Defenders should ensure the following logging is enabled across endpoints.
- Process creation logging
- LSASS access monitoring
- PowerShell script block logging
- Network connection telemetry
These signals are typically captured using Sysmon or EDR platforms.
Identity and authentication telemetry
Because identity abuse is central to the campaign, authentication telemetry is equally important. Defenders should monitor for:
- Abnormal RDP authentication patterns
- Administrative logons outside normal activity windows
- Authentication events across multiple hosts in short time periods
These patterns often provide early indicators of lateral movement.
Endpoint management visibility
Modern destructive campaigns sometimes attempt to leverage endpoint management platforms as a distribution channel. If organisations use Microsoft Intune, defenders should ensure monitoring of:
| Control | Detection Purpose |
|---|---|
| Device configuration audit logs | Detect policy changes |
| Device compliance logs | Detect abnormal device states |
| Application deployment logs | Detect malicious software distribution |
| Administrative activity logs | Detect privilege abuse |
These signals help defenders detect attempts to abuse management infrastructure for payload deployment.
Behaviour Chain Observed in the Campaign
When analysing incidents like this, it helps to step back and look at the sequence of activity. The most common pattern looks like this:
Credential Dump
↓
Privileged Session Creation
↓
RDP Lateral Movement
↓
Group Policy Payload Distribution
↓
Destructive Impact
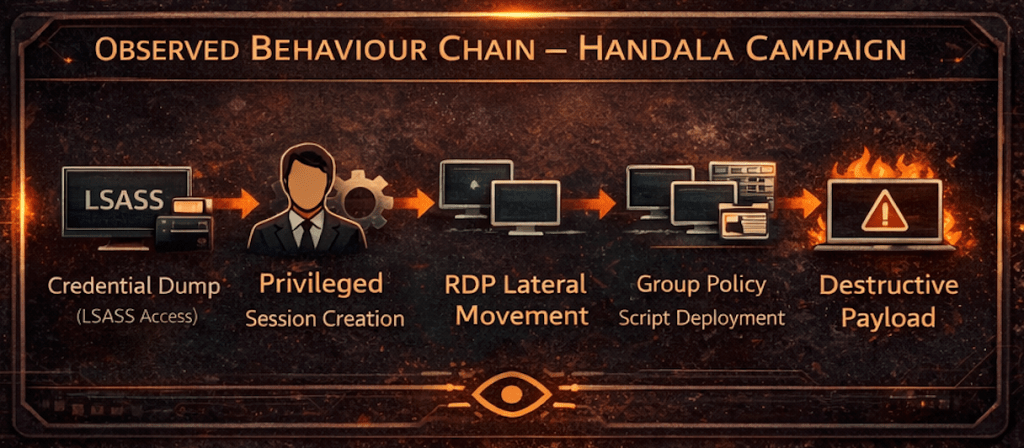
The earlier defenders detect this chain, the greater the chance of preventing the final stage. This observation forms the basis of the detection analytic below.
Experimental Detection Analytic
Rather than detecting specific tools, the following Sigma rule focuses on behaviour that attackers cannot easily change. It detects LSASS credential dumping activity followed by remote logon behaviour.
title: TEI Behaviour Chain - LSASS Dump Followed by Lateral Movementid: tei-sigma-001status: experimentalauthor: ThirdEye Intel / SOCtane Intelligence Frameworkdescription: Detects LSASS credential dumping via rundll32 comsvcs MiniDump followed by remote logon activity.logsource: product: windowsdetection: lsass_dump_activity: Image|endswith: '\rundll32.exe' CommandLine|contains: - 'comsvcs.dll' - 'MiniDump' remote_logon_activity: EventID: 4624 LogonType: - 3 - 10 condition: lsass_dump_activity or remote_logon_activityfields: - Image - CommandLine - User - LogonType - IpAddress - WorkstationNamelevel: criticalThis analytic focuses on the earliest stages of the intrusion chain. Detecting these behaviours provides defenders an opportunity to intervene before destructive payloads are deployed.
Defender Takeaway
Campaigns like this rarely begin with destructive actions. They begin quietly.
- Credentials are extracted.
- Sessions are created.
- Movement spreads across the network.
By the time destructive activity becomes visible, the intrusion is already well established. The organisations that stop these attacks are not the ones that detect the final stage. They are the ones that detect the behaviours leading up to it.
What Comes Next
Threat actors will continue to evolve their tooling, but their objectives rarely change.
- They still need access.
- They still need movement.
- They still need control.
And those behaviours leave traces. For defenders, the real advantage comes from turning intelligence into detection before the attack begins.







Leave a comment